The FBI Agent who arrested Epstein had his computer "hacked" resulting in 100TB of files missing forever
How a Foreign Intruder Walked Into the FBI’s Most Sensitive Epstein Files, and the Agent in the middle of it all
Your subscription truly helps share this work.
The morning after Super Bowl Sunday, Aaron Spivack walked into the FBI’s New York Field Office and sat down at his computer. It had seemingly restarted overnight. He sat down, he noticed a text file had opened by itself — or rather, someone had left a message for him — ‘Your network has been compromised’
— EFTA00173598
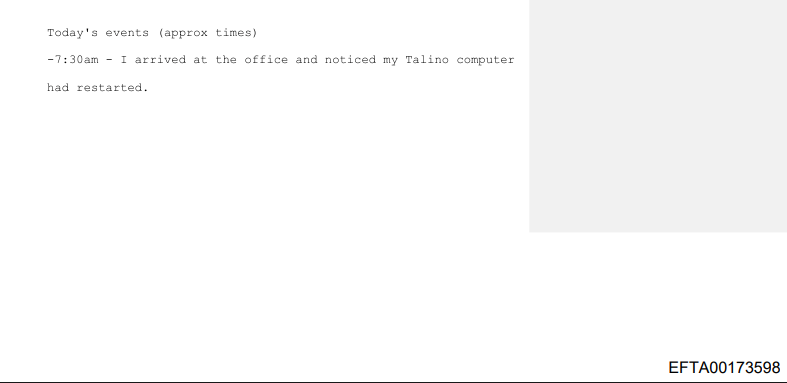
The timeline begins: ‘7:30am - I arrived at the office and noticed my Talino computer had restarted.’ Written the same day as the breach discovery.
Source: EFTA00173598–99
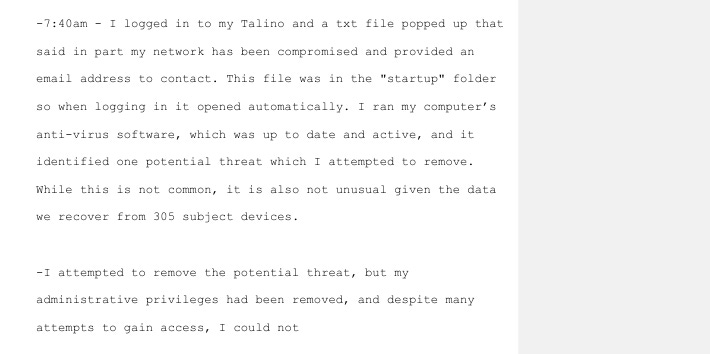
By 7:40 am, Spivack was logged in. That’s when the text file opened itself — right from his startup folder. Someone had been inside his computer. The message was short but to the point — his network was compromised, they left an email address for him to contact.
He ran antivirus software. He called CART, the FBI’s computer analysis response team, and he called Synology, the server manufacturer. For hours, Spivack assumed it was a hardware failure. A glitch. Something routine. Right.
It wasn’t until 3:30 that afternoon when he and Christian Idsola from CART finally started combing through the log files that they saw it.
Strange IP activity, two addresses.
In his own words, written in his own timeline that morning: the activity included “combing through certain files pertaining to the Epstein investigation.” By 5:00 pm, Spivack wrote five words: “we realized we were hacked.”
But, there was something he didn’t write in that February 13 timeline, something nobody outside the FBI would know for three years — Aaron Spivack wasn’t just some agent whose server got breached — he was the agent who had arrested Jeffrey Epstein himself at Teterboro Airport. The agent who had searched Epstein’s Manhattan townhouse, and the agent assigned to search Little St. James island. Aaron Spivack, the agent who had worked the Epstein case from arrest to death, to aftermath, was hacked?
Agent Aaron Spivack
Source: EFTA00147199–EFTA00147208 Primary document
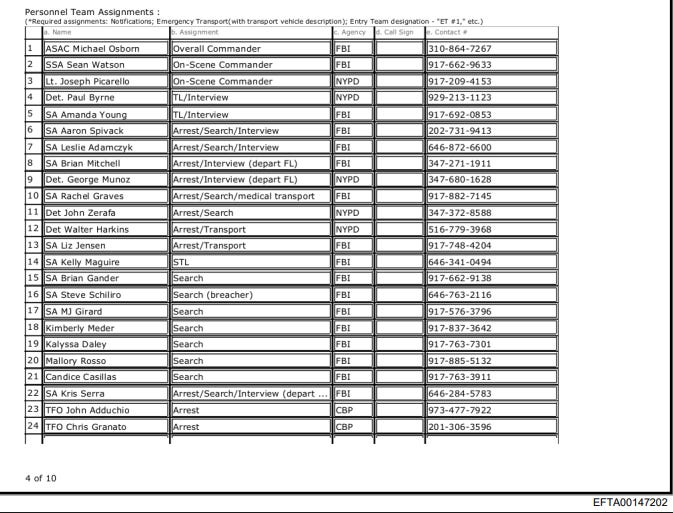
The FBI doesn’t do anything small, as we know. The operations order for Jeffrey Epstein’s arrest — July 6, 2019 — runs 10 pages long.
It names the intercept point, Teterboro Airport, 111 Industrial Avenue, Bergen County, New Jersey. It also names the backup point, 9 East 71st Street — Epstein’s townhouse, the vehicle — a 2016 black Chevrolet Suburban, and the plan: CBP stops Epstein when his plane touches down at 5:20 pm, FBI and NYPD move in, then they search the Manhattan house. Page after page of procedure. And there, sixth on the personnel list, under “Arrest/Search/Interview,” is a name — SA Aaron Spivack.
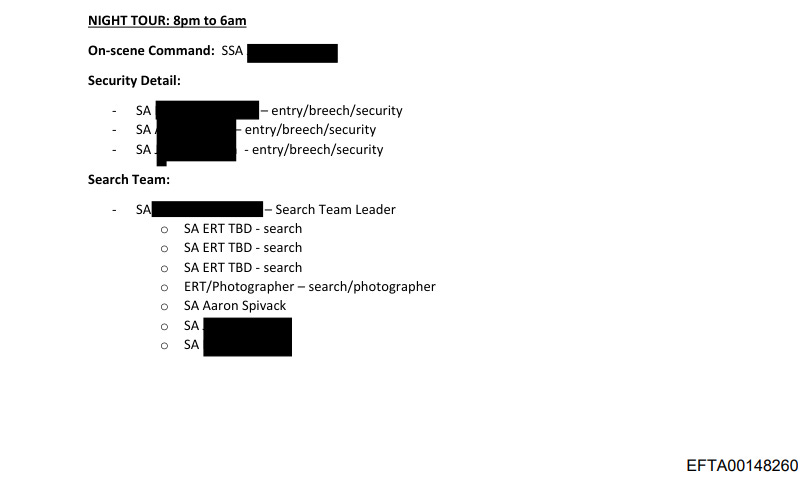
Operations order for the island search. Spivack on the Night Tour (8pm–6am) search team. SDNY had been drafting the island search warrant as early as August 6, 2019 — four days before Epstein’s death.
Source: EFTA00148259–EFTA00148261
A month later Spivack got a new assignment: Little St. James, Epstein’s infamous private paedophile island in the U.S. Virgin Islands.
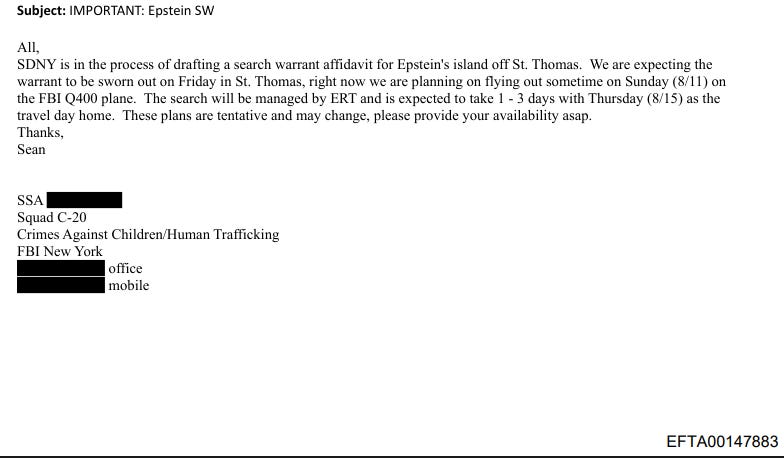
The operations order for that search warrant puts him on the Night Tour search team, the team that would comb through Epstein’s island after dark. But here’s the thing, the email organizing that search — EFTA00147883 dated August 6, 2019 — was sent by SSA Sean Watson to Spivack and the full C-20 team while Epstein was still alive.
Jeffrey Epstein was found dead in his cell on August 10 2019, at the Metropolitan Correctional Center in Lower Manhattan NY. The search went ahead anyway and Spivack was on the team that picked through Epstein’s island while Jeffrey Epstein’s body was still at the medical examiner’s office.
Watson writes: ‘SDNY is in the process of drafting a search warrant affidavit for Epstein’s island off St. Thomas. We are expecting the warrant to be sworn out on Friday in St. Thomas.’ Spivack is cc’d directly.
Source: EFTA00147883
Spivacks Career
Aaron Spivack joined the FBI in 2006 as an intelligence analyst. Two years later he became a Special Agent and by 2010 he was assigned to squad CY-3: the child exploitation and cyber unit. By 2017 he had taken over the squad’s Group I undercover operation and doubled its output. In his sworn statement he claimed to have personally rescued ‘hundreds of children from exploitation.’ The FBI certified him as an ‘expert witness in child exploitation’ — for the entire bureau. He received the FBI’s Medal of Excellence not once but twice.
By any institutional measure, Aaron Spivack was one of the bureau’s most effective child exploitation investigators and he was also the agent running a forensic lab with no dedicated IT support, no information security officer, disabled antivirus software, and a network he had configured himself by following instructions he found on Google. The math ain't mathing here folks once again in the Epstein saga that never ends.
The Door Was Wide Open
Statement runs EFTA00173481 through EFTA00173568 (clean version) and EFTA00173569 through EFTA00173632 (draft with attorney margin comments visible). Sworn September 2024. Attorney: Richard J. Roberson Jr.
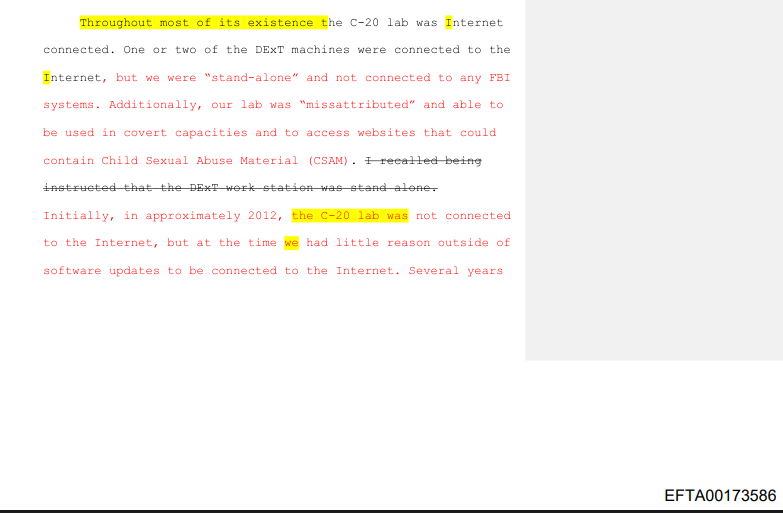
Source: EFTA00173586–88
The C-20 computer lab sat on the 10th floor of the FBI’s New York Field Office. It wasn’t supposed to exist the way it did. It started as a single forensic workstation for child exploitation evidence. Offline, unconnected, and isolated. No FBI network, no internet, safe, how it should be. Over time, the job changed. Software required cloud licenses and evidence had to be uploaded to the National Center for Missing and Exploited Children through an online portal. The lab needed internet. So they asked for help – but nobody at the FBI would help them.
Anthony Broderick, the NYFO CART networking person, told Spivack to ‘read the manuals’ and said he didn’t have the ‘bandwidth to help.’ So Spivack did what any agent with no training, no support and no budget would do — he Googled it. Meanwhile, the FBI told him to disable the antivirus on the lab computers. A new forensic cloud based program called Axiom kept getting flagged as a threat and instead of fixing the software itself they just killed the antivirus entirely and operated without any protection or firewalls.
Now for the computers. The NAS storage units, and the RAID tower — all of which contained CSAM from active investigations — were all connected to the internet when they had not been before. The antivirus was disabled, in a room without a keypad lock apparently, because the locksmith said there was no funding for one.
And here’s the real kicker, until approximately February 2023, just weeks before the breach, the New York Field Office didn’t even have a designated Information System Security Officer. The position was required and it had sat empty for years.
“Until approximately February 2023, the NYFO did not have a designated Information System Security Officer (ISSO). This is a required position, and I think it being left unfilled exacerbated many of the problems that are discussed herein.”
— Aaron Spivack EFTA00173582
The door wasn’t just open – it had been hanging off its hinges for years
In late 2022 or early 2023, Spivack tried to set up Microsoft’s Remote Desktop Protocol on the lab computers. The idea made sense: forensic jobs that ran over weekends could be nudged along remotely. He wouldn’t have to drive into the NYFO every time anymore… convenient.
His supervisor’s supervisor, SSA Heath Graves — the DExT Program Manager at FBI headquarters — encouraged the idea. The Microsoft setup instructions, Graves said, were easy to follow. So, Spivack set it all up on his own. He thought the security was blocking his remote access attempts. He had just opened the lab’s RDP port to the outside world and didn’t know it.
Spivack: “I thought the C-20 system was secure. I attempted to access the C-20 computer lab through RDP. I believed the lab’s security prevented me from remoting in. I had no idea that in doing so I had opened the lab’s RDP port and that it had worked.”
— EFTA00173595–96
Later, someone would tell him the configuration was “mostly correct” and that he was just a step or two away from having set it up securely.
But, at that point, it was too late.
SUPER BOWL SUNDAY — THE BREACH
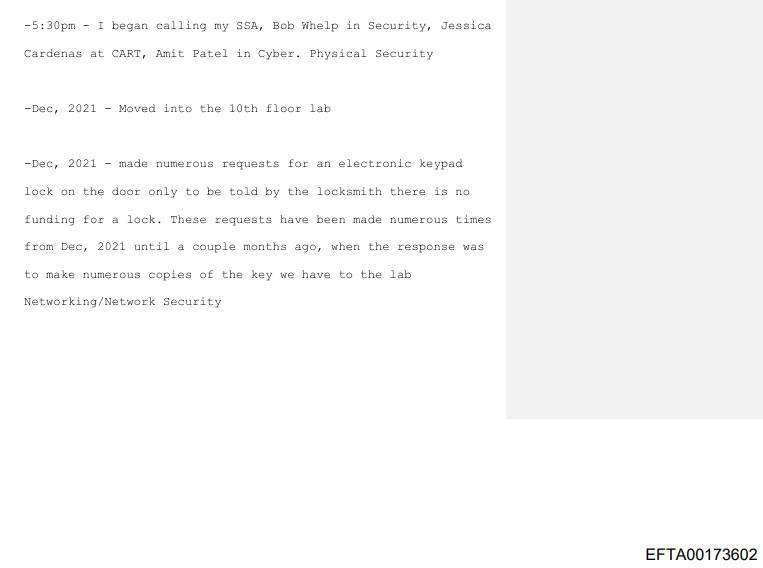
Source: EFTA00173598–EFTA00173602 — Timeline sent to SSA Seamus Clarke the day of discovery. Covers 7:30 AM through 5:30 PM. Ends: ‘5:30pm - I began calling my SSA, Bob Whelp in Security, Jessica Cardenas at CART, Amit Patel in Cyber.’
February 12, 2023. Super Bowl Sunday.
Millions of people were watching the game. But somewhere out there, someone was watching something else — a screen, a server, a literal unlocked door.
Using an IP address on TMobile’s network, they found an open RDP port on a server inside the FBI’s New York Field Office. They didn’t break in, they just walked through. Then, they started looking around.
The server held CSAM from active investigations and it also held files from the Epstein case. The intruder* began combing through them.
At some point, they realized what they were looking at — or thought they did. They believed they had hacked into a criminal’s server. Someone holding abuse material. Someone who should be reported to the FBI — someone who could be easily blackmailed for personal gain.
They did not realize they had actually just hacked the FBI itself.
Spivack’s timeline, written the next morning: “7:40am - I logged in to my Talino and a txt file popped up that said in part my network has been compromised and provided an email address to contact. This file was in the ‘startup’ folder so when logging in it opened automatically.”
— EFTA00173598
By 5:00 pm, Spivack and his colleague Christian Idsola had confirmed that they’d been hacked. By 5:15, they’d shut everything down, saved the logs, and killed the internet that should never have been connected in the first place. By 5:30, Spivack was on the phone — his SSA, Security, CART, Cyber.
Then they saw the damage… 500terabytes of data — gone and deleted. Spivack managed to recover about 400 of it (he was again told to Google how) he says. You just can’t make this stuff up.
“500 terabytes of data was gone as a result of the intrusion. I was able to recover about 400 terabytes of that data, however. I was told to Google how to recover the data. No one else tried to help us.”
— EFTA00173603–04
The OCIO Section Chief, Matt Smith, was apparently pissed. He found an email Spivack had sent before the intrusion — a request for help. No one had responded.
THE HACKER
The DOJ docs tell us that the breach happened and when it happened. The Epstein files were accessed by an unknown hacker, the massive amount of data loss. Spivack’s own account on the matters — but everything else? That comes from one anonymous source who spoke to Reuters.
According to that source, the intruder was likely a foreign cybercriminal acting alone — not a state sponsored spy. They didn’t realize they had hacked the FBI, they thought they’d stumbled into a criminal’s server, a cache of CSAM. And they were disgusted, just vigilante justice, right?
The same source told Reuters that FBI officials made contact with the hacker and convinced them to join a video call, where they then “flashed their credentials” on camera.
The hacker’s identity? Unknown. Country of origin? Unknown. Current status? Unknown. No arrests have been announced and the FBI called it an “isolated cyber incident.”
NOTE: The video call, the hacker’s disgust, the “lone foreign actor” characterization — all of it comes from a single anonymous source. LPF cannot independently verify these details. They are presented here as attributed to Reuters, not as primary document fact. What IS primary-documented: the breach happened. The date. The RDP vulnerability. The Epstein file access. The two IPs. The data loss. Spivack’s own account. That’s the foundation here.
SPIVACK’S DEFENSE
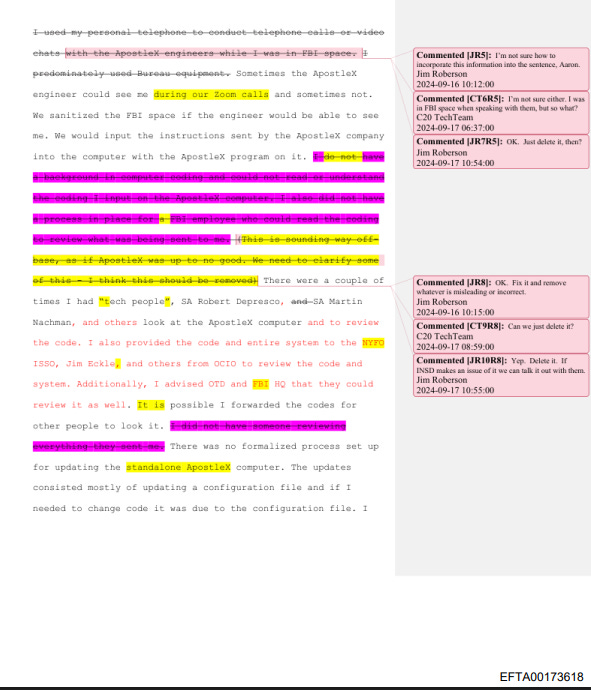
Source: EFTA00173618 / EFTA00173588 — The draft statement (EFTA00173569–EFTA00173632) contains visible tracked changes and comment bubbles from attorney Jim Roberson and a reviewer identified as ‘C20 TechTeam.’ Comments include: ‘OK. Just delete it.’ and ‘I’m not sure how to incorporate this.’ The editorial process is preserved in the document itself.
Over two different days, months apart — January 26, 2024 and August 8, 2024 — Spivack gave his sworn statement to the FBI’s Inspection Division. His attorney, Richard J. Roberson Jr, listened in by phone both times.
The statement runs dozens of pages, LPF has two versions: a clean signed copy and a draft. The draft is where it gets interesting.
In the margins, Roberson and a reviewer called “C20 TechTeam” are debating what to keep and what to cut out. Real time edit preserved in the document itself.
“OK. Just delete it.”
“I’m not sure how to incorporate this.”
“Excellent!”
“I modified this a little. Want to chat with you about it later.”
You can see the lawyers trying to shape the story while Spivack tells it.
His core argument is simple. He was never a system administrator, he was a child exploitation agent. He was told to build a network and given no help. Given no budget. He was told by headquarters to follow Microsoft’s instructions on Google. Then investigated when the network got hacked.
“Since the intrusion, my squad mates and I have been referenced as having been ‘System Administrators’, which we absolutely are not. The INSD report identifies me, and others on my squad, as having been System Administrators despite the fact we were not, have never been trained in system administration, and were never qualified to be system administrators.”
Spivack — EFTA00173629
And then there’s this:
“I understand I opened the C-20 lab’s RDP ports, but the FBI knew what I was doing. The FBI had told me to follow the instructions on Microsoft website on how to open the ports.”
— EFTA00173604
He’s not denying he opened the door but he is saying the FBI watched him do it.
More Institutional Failure
The most important detail in Spivack’s statement isn’t what he did, it’s what the FBI admitted afterward.
“FBI HQ Criminal Investigative Division (CID) DAD Jose Perez has since acknowledged the policy for the lab was vague or non-existent, which is something he advised me of in an email that I provided to the interviewing Agents. Additionally, a few weeks after the intrusion, DAD Perez, with others from FBI HQ, were visiting the NYFO on un-related matters, however there was a meeting to discuss the status of the intrusion which I was present for. Prior to the meeting, DAD Perez, whom I have known for years, approached me and informed me that he knew I was not responsible for the intrusion. DAD Perez further advised me that our lab was one of many across the FBI that had similar configurations.”
Spivack — EFTA00173538–39
Read that again. A Deputy Assistant Director of the FBI walked up to Spivack weeks after the breach and told him, face to face:
I know you’re not responsible. Your lab was one of many across the bureau with the same security holes.
If one server could be breached, others could have been too. And who knows what kind of secure data has already slipped into the hands of unknown forces around the world.
The FBI has never disclosed any additional breaches.
What Was On His Server
Now, the simplest question has no answer — what files did the hacker actually see?
Spivack’s statement confirms the server held evidence from his active cases, and those cases included the Epstein investigation.
An email from December 14, 2020. An agent writing to their supervisor about teleworking: “I’ll be working on a few research scrubs for 305 cases (spivack).” Two years before the breach. Long after Epstein was dead. Spivack’s case files were still active.
— EFTA01653690
The breached server sat in the Child Exploitation Forensic Lab, it held working copies of evidence from multiple child exploitation investigations, and it held files from the Epstein case. It had been connected to the internet, stripped of antivirus, and left accessible through an open RDP port.
Georgia Tech professor Jon Lindsay told Reuters:
“Who wouldn’t be going after the Epstein files if you’re the Russians or somebody interested in kompromat? If foreign intelligence agencies are not thinking seriously about the Epstein files as a target, then I would be shocked.”
Whether the hacker who found that open port on Super Bowl Sunday was a state actor, a hacktivist, or just a lone cybercriminal — they found what they were looking for. Or, they stumbled onto something nobody was ever supposed to find.
500TB of Epstein Library data deleted. 100TB of that never recovered. Epstein investigation files accessed by an unknown party, from an unknown country. The investigation remains open and no arrests have been made.
The Bottom Line
The FBI called it an isolated cyber incident, but DAD Perez told Spivack, face to face, that his lab was one of many with the same broken configuration. Both things cannot be entirely true.
The Epstein files remain the most politically sensitive law enforcement archive in the United States. A foreign hacker walked through an open door and spent a day inside them. And that door had been left open by the same agent who arrested the man the files were about.
That is not a conspiracy. That is a documented institutional failure — once again — preserved in the files themselves — signed and sworn by the man at the center of it.
“I love this job. I was not reckless. There was no self-interest involved. I was always trying to do the right thing.”
— Aaron Spivack, sworn statement, September 2024
Truth is, this work takes all of us.
If this investigation has been useful to you — if it gave you something to think about, something to share, something to act on — consider supporting Last Page First. Independent investigative journalism doesn’t have institutional backing behind it. It has the readers ♥
Have a tip? A lead you want to share?
This work is entirely reader supported. No grants, no advertisers, no editorial board — just primary documents and the time it takes to read them. If you want to keep this going, donating is the most direct way to help. Thank you.
Sources
EFTA00148259–00148261 — Operations order for island search. Spivack on Night Tour search team.
EFTA01653690 — December 2020 telework email referencing ‘research scrubs for 305 cases (spivack).’
The hacker’s identity, country of origin, the video call, the expressed disgust, and the lone/foreign characterization are ATTRIBUTED to Reuters’ anonymous source only. Not in any EFTA document reviewed by LPF.


Not buying this for a second. All federal government agencies computers have firewalls, especially those storing sensitive data. They are backed up daily. This story of a possible hack is total rubbish.
So some entity has the entirety of the major investigative and procedural paperwork that was generated to charge and arrest Epstein. That information is worth a lot of money . Step right up.